YOUR ENCRYPTED COMMS ARE IN ADVERSARY ARCHIVES
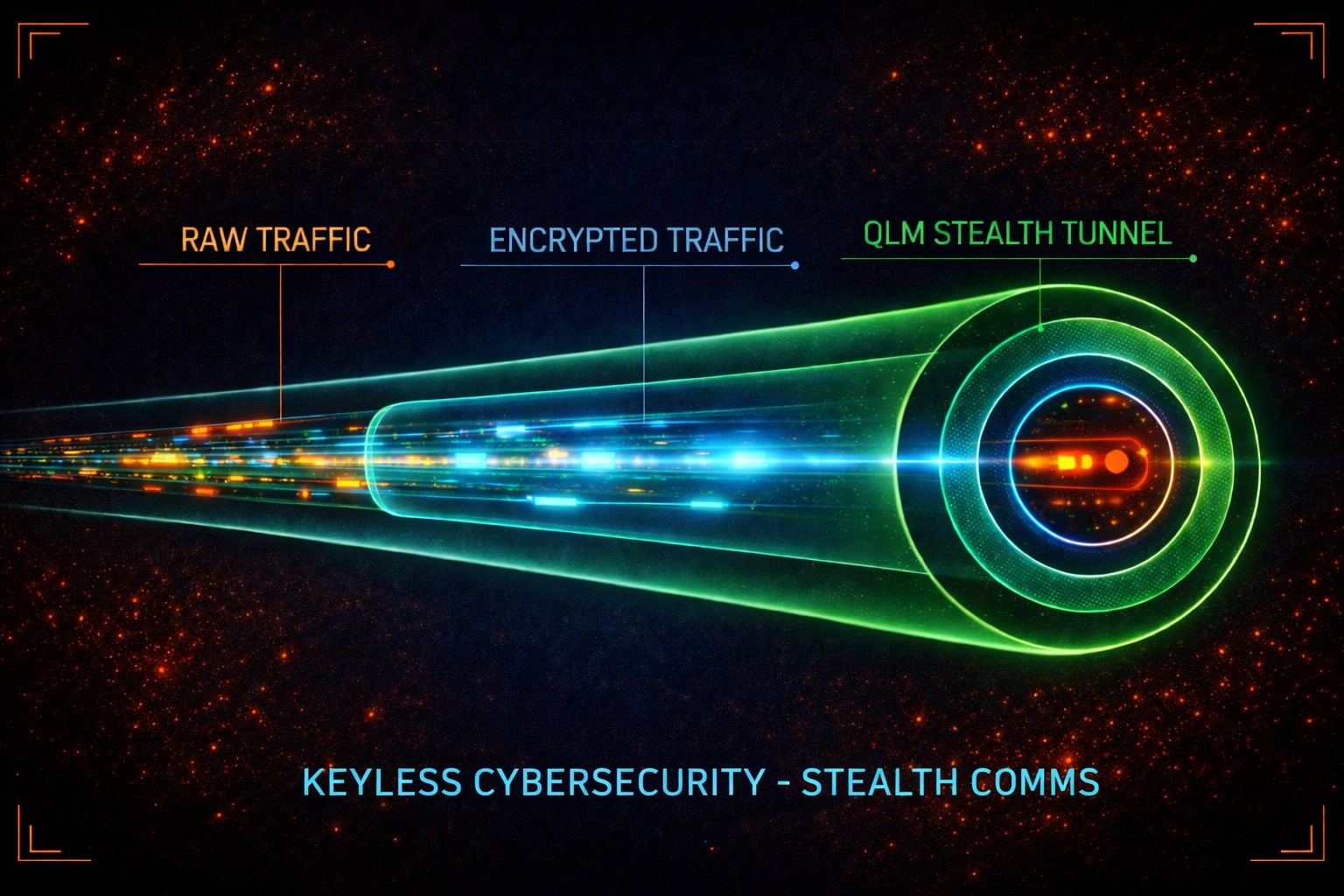
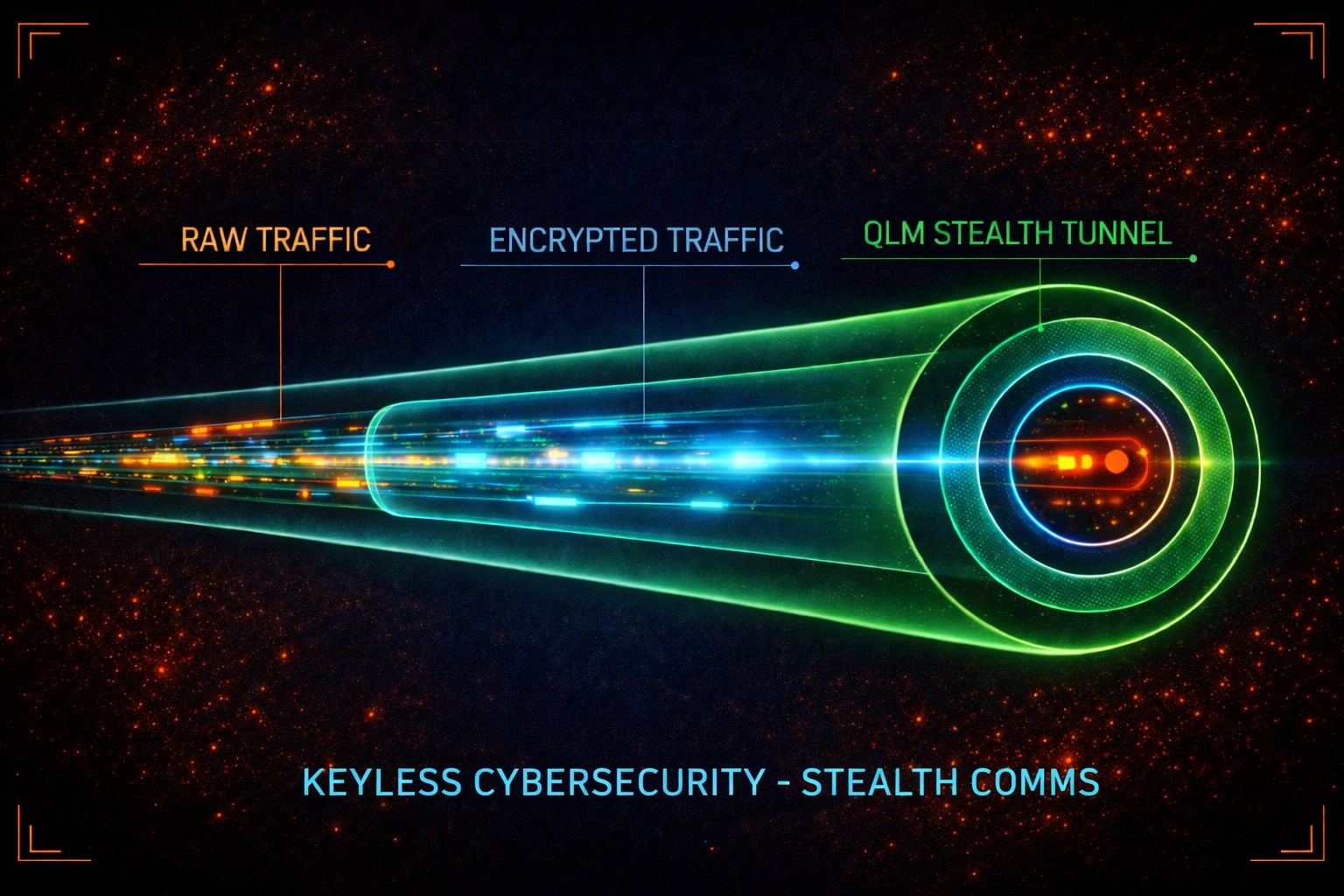
COMMS—MADE STEALTH
Capture is inevitable. Leverage isn't. Zero Keys.
QUANTUM PARADIGM SHIFT
YOUR ALGORITHM ISN'T THE PROBLEM. YOUR KEY MATERIAL IS. COPIES IN THE FIELD. COPIES IN ESCROW. COPIES ON SYSTEMS YOU FORGOT EXISTED. BREACHES DON'T START WITH WEAK CIPHERS. THEY START WITH KEY EXPOSURE. WE REMOVED THE KEY DOMAIN. NOTHING TO GENERATE. NOTHING TO DISTRIBUTE. NOTHING TO ROTATE. NOTHING TO STEAL. NOTHING TO HACK.
QUANTUM PARADIGM SHIFT
YOUR ALGORITHM ISN'T THE PROBLEM. YOUR KEY MATERIAL IS. COPIES IN THE FIELD. COPIES IN ESCROW. COPIES ON SYSTEMS YOU FORGOT EXISTED. BREACHES DON'T START WITH WEAK CIPHERS. THEY START WITH KEY EXPOSURE. WE REMOVED THE KEY DOMAIN. NOTHING TO GENERATE. NOTHING TO DISTRIBUTE. NOTHING TO ROTATE. NOTHING TO STEAL. NOTHING TO HACK.
QUANTUM PARADIGM SHIFT
YOUR ALGORITHM ISN'T THE PROBLEM. YOUR KEY MATERIAL IS. COPIES IN THE FIELD. COPIES IN ESCROW. COPIES ON SYSTEMS YOU FORGOT EXISTED. BREACHES DON'T START WITH WEAK CIPHERS. THEY START WITH KEY EXPOSURE. WE REMOVED THE KEY DOMAIN. NOTHING TO GENERATE. NOTHING TO DISTRIBUTE. NOTHING TO ROTATE. NOTHING TO STEAL. NOTHING TO HACK.
WHY ZERO keys?
ONE KEY RECOVERED. YEARS OF TRAFFIC EXPOSED. That is the risk model of key-based systems. We removed the model entirely: NO KEY-RECOVERY PATH. NO ROTATION WINDOWS. NO ESCROW EXPOSURE. NO DISTRIBUTION CHAIN. No Keys on the Wire. No key to recover. No past to decrypt.
WHY ZERO keys?
ONE KEY RECOVERED. YEARS OF TRAFFIC EXPOSED. That is the risk model of key-based systems. QLM® removes the model entirely: NO KEYS ON THE WIRE. NO KEY-RECOVERY PATH. NO ROTATION WINDOWS. NO ESCROW EXPOSURE. NO DISTRIBUTION CHAIN. No key to recover. No past to decrypt.
WHY ZERO keys?
ONE KEY RECOVERED. YEARS OF TRAFFIC EXPOSED. That is the risk model of key-based systems. QLM® removes the model entirely: NO KEYS ON THE WIRE. NO KEY-RECOVERY PATH. NO ROTATION WINDOWS. NO ESCROW EXPOSURE. NO DISTRIBUTION CHAIN. No key to recover. No past to decrypt.
WHY ZERO keys?
ONE KEY RECOVERED. YEARS OF TRAFFIC EXPOSED. That is the risk model of key-based systems. We removed the model entirely: NO KEYS ON THE WIRE. NO KEY-RECOVERY PATH. NO ROTATION WINDOWS. NO ESCROW EXPOSURE. NO DISTRIBUTION CHAIN. No key to recover. No past to decrypt.
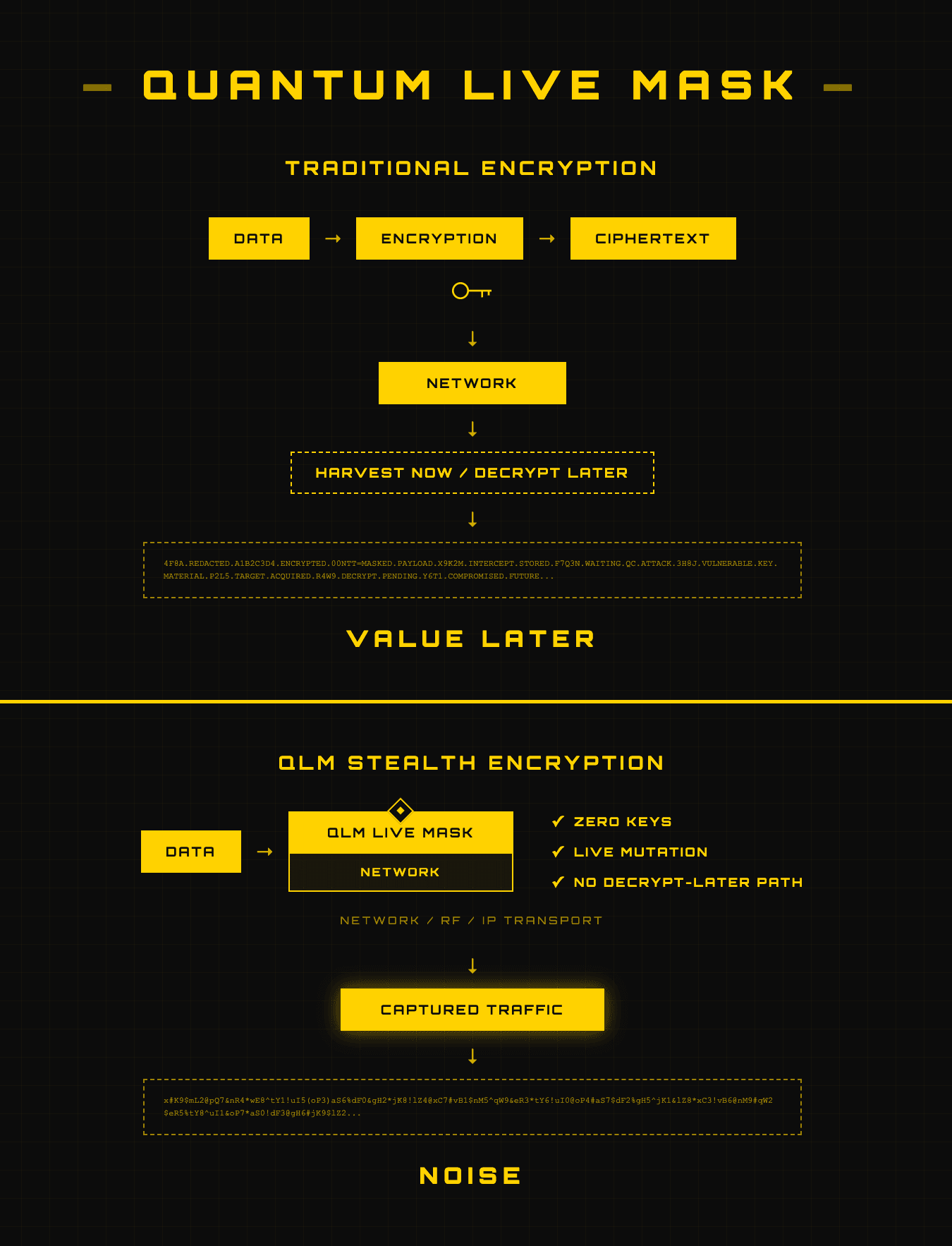
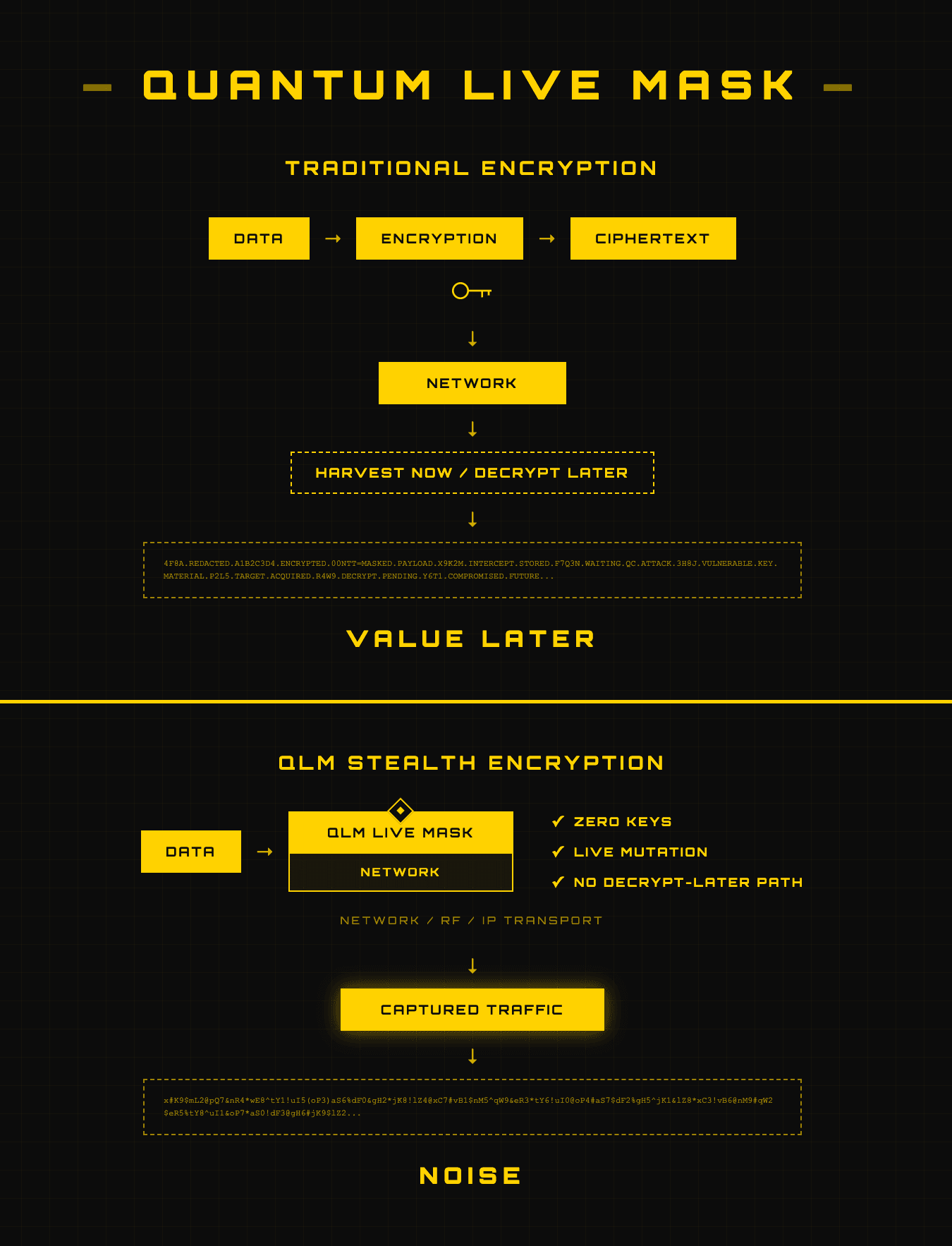
/ HARVEST NOW - DECRYPT LATER. SOLVED.
The Day Stored Data Becomes Readable Is the Day Your Sovereignty Ends
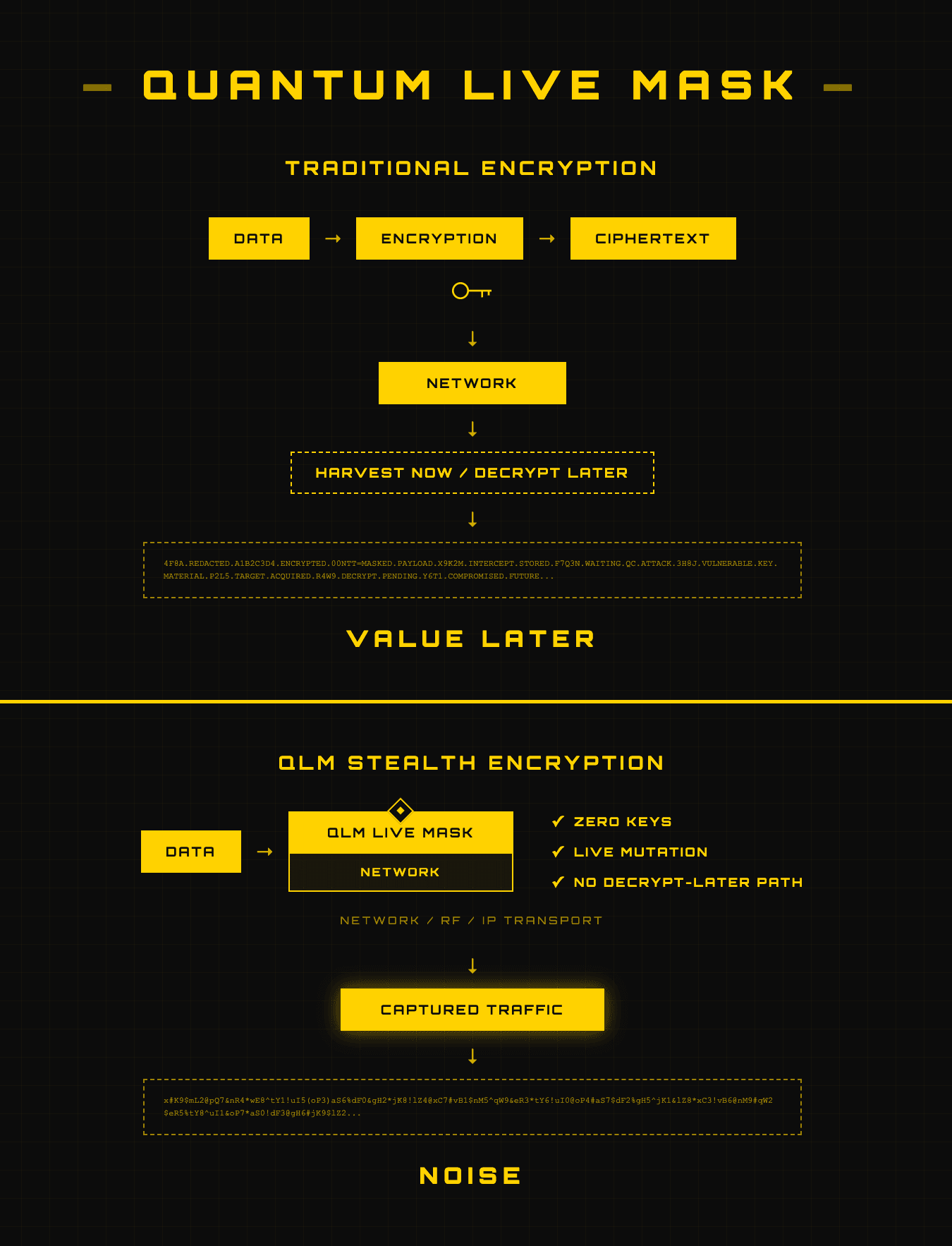
/ QUANTUM LIVE MASK
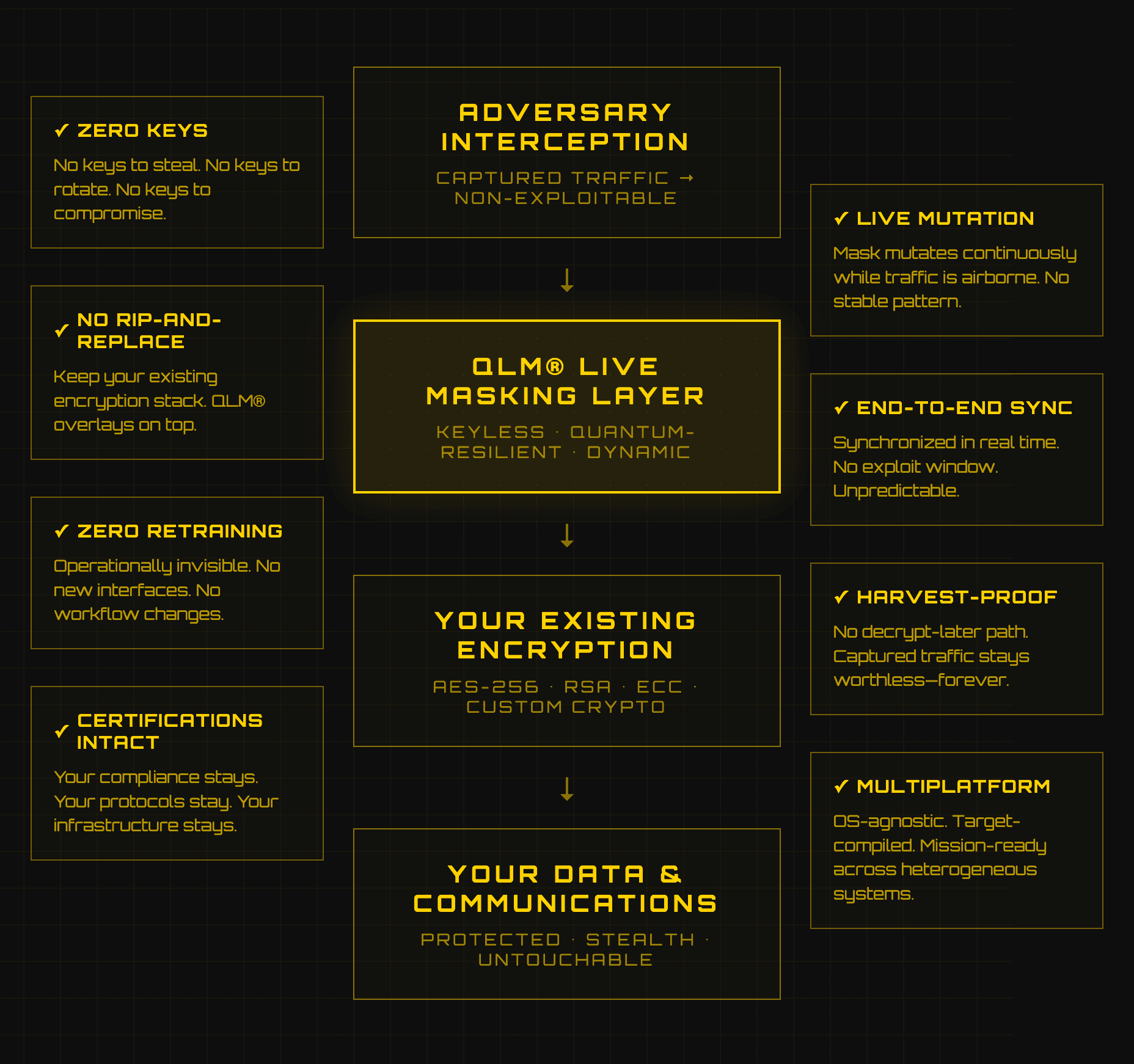
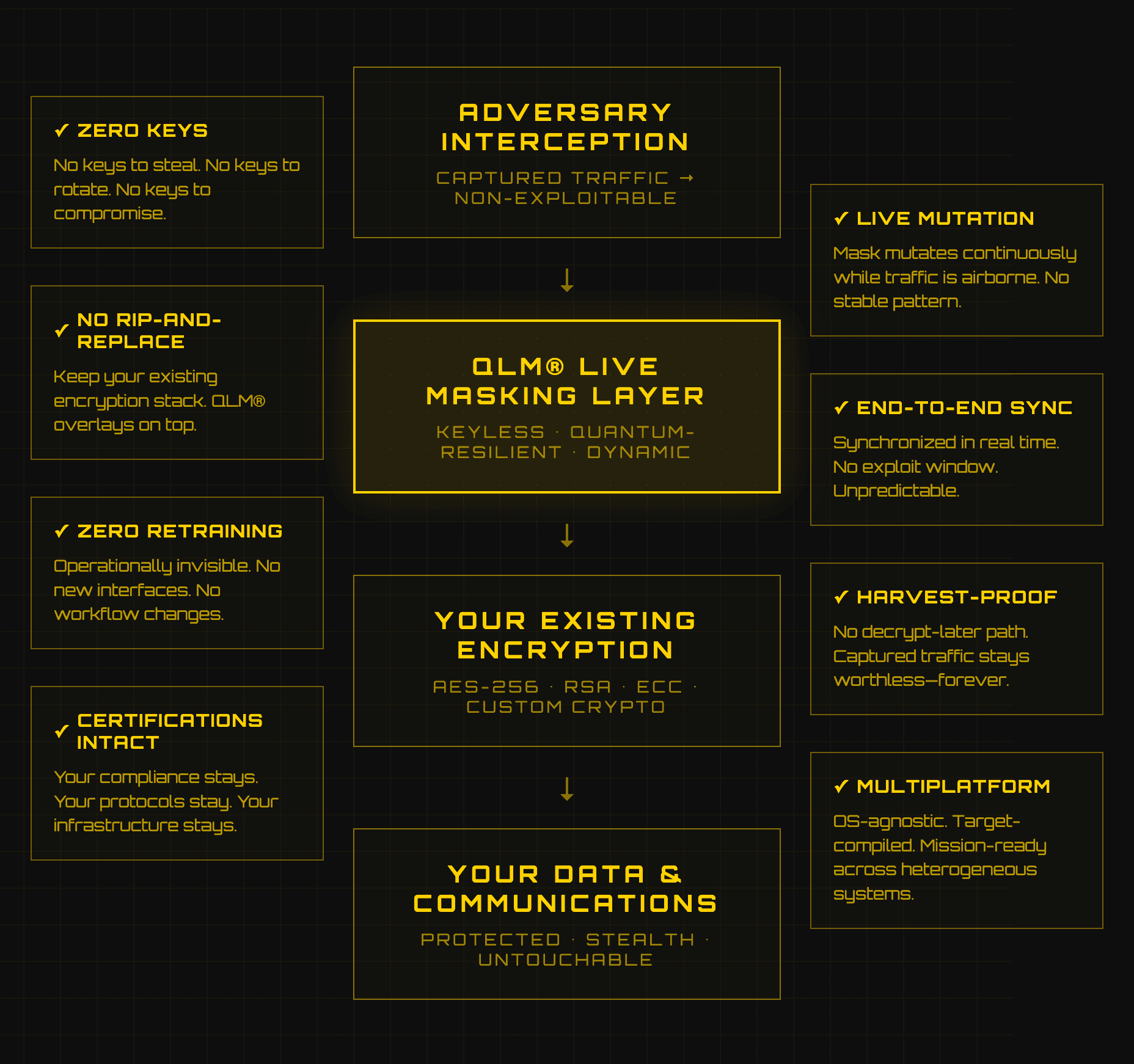
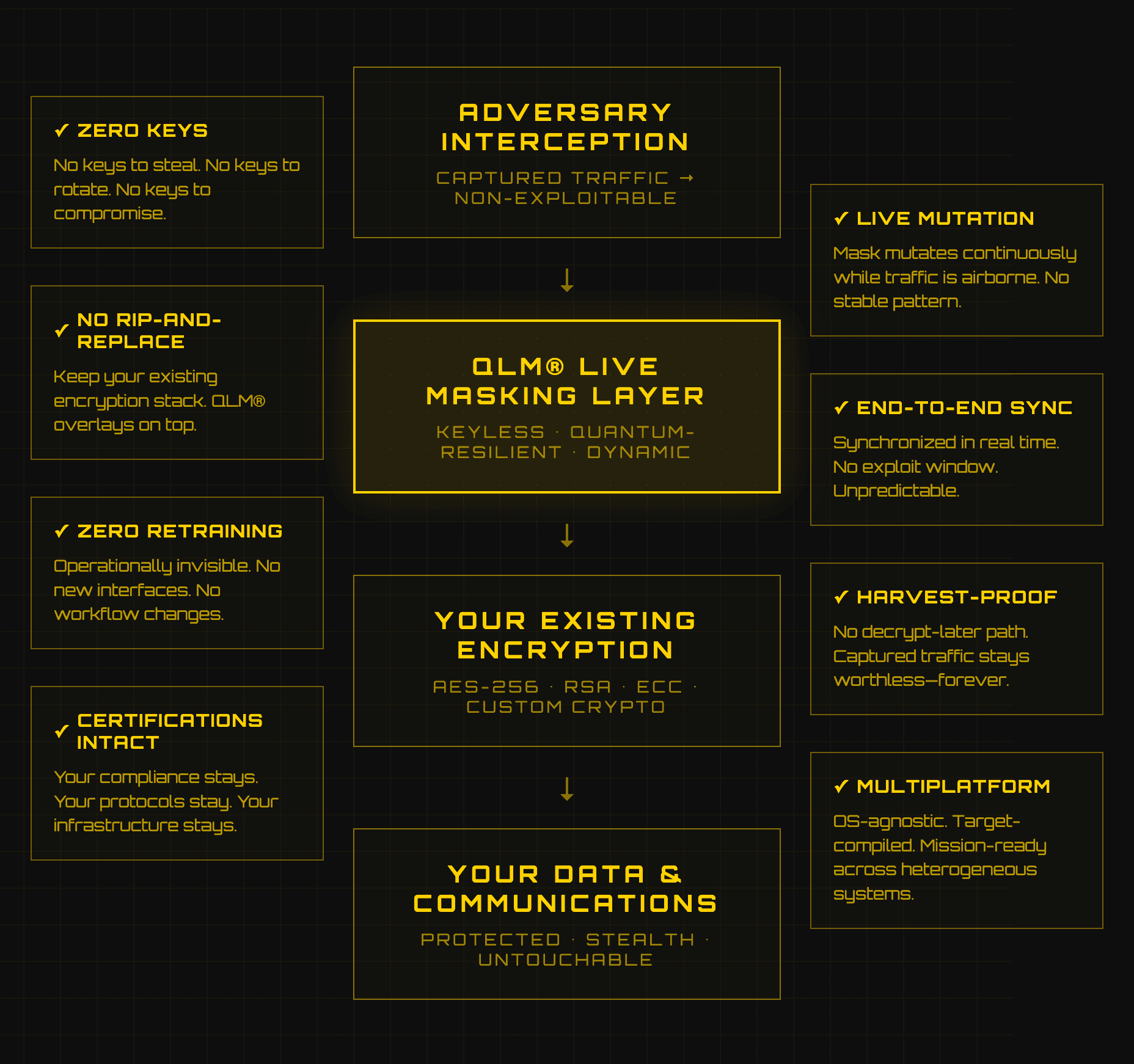
Three words. One disruptive model. MILITARY-GRADE. POST-QUANTUM CYBERDEFENSE. QLM® (Quantum Live Mask) is a keyless, quantum-resilient live-masking layer that wraps your existing encrypted traffic inside a stealth tunnel — with no keys on the wire and no changes to your certified stack. Capture it. No recoverable plaintext. Harvest Now, Decrypt Later. Solved. / QUANTUM Quantum Computers threaten security by targeting key material. We removed the key domain entirely. No keys to steal. No keys to recover. No keys to break. Nothing to hack. / LIVE The mask mutates continuously while traffic is in the air. Synchronized end-to-end, in real time. No stable pattern. No exploit window. Unpredictable. alive. / MASK A keyless channel-level overlay that creates a stealth tunnel around your existing encrypted traffic. No keys on the wire. No rip-and-replace. AES-256. RSA. ECC. Custom crypto. If it's key-based, QLM® wraps it. No session keys in transit. No harvest-now, decrypt-later path. Captured traffic stays worthless.
/ THE QUANTUM THREAT
/ LOSE A KEY ONCE YOU LOSE YEARS OF COMMS — RETROACTIVELY. VULNERABLE DOESN’T MEAN WEAK. IT MEANS OBSOLETE. YOUR ALGORITHMS GET SUNSET. YOUR STACKS GET REPLACED. EVEN SUITE A LINEAGES ARE BEING RETIRED. / THE REAL ATTACK IS HAPPENING TODAY YOUR ADVERSARY IS HARVESTING TRAFFIC NOW. STORING EVERYTHING. WAITING FOR QUANTUM TO TURN “CLASSIFIED” INTO “ARCHIVED.” ONE COMPROMISE TURNS TODAY’S INTERCEPTS INTO YEARS OF ARCHIVED EXPOSURE. BY THE TIME QUANTUM BREAKS RSA/ECC AT SCALE, YOUR WINDOW IS CLOSED. NOT JUST TECHNICALLY. CONTRACTUALLY. OPERATIONALLY. POLITICALLY. YOU DON’T NEED “STRONGER” ENCRYPTION. YOU NEED COMMS THAT CAN’T BE DECRYPTED TOMORROW. / IMAGINE A WORLD WHERE YOUR ADVERSARY CAPTURES EVERY PACKET. STORES EVERY FRAME. RUNS IT THROUGH THE MOST ADVANCED QUANTUM PROCESSOR EVER BUILT AND RECOVERS NOTHING. NOT BECAUSE YOUR ENCRYPTION WAS STRONGER. BECAUSE THERE WAS NO KEY TO RECOVER. NO KEY WAS EVER GENERATED. NO KEY WAS EVER EXCHANGED. NO KEY WAS EVER STORED. YOU CAN’T BREAK WHAT DOESN’T EXIST. CAPTURE EVERYTHING. DECRYPT NOTHING. REMOVE THE EXPIRY DATE FROM YOUR STACK — IN WEEKS, NOT YEARS. / STEALTH QUANTUM LAYER STRATEGY THE B-2 STEALTH BOMBER DIDN’T ADD ARMOR. IT BECAME UNDETECTABLE. WE DO THE SAME FOR ENCRYPTED COMMS: NOT STRONGER, STEALTH. AS LONG AS A KEY EXISTS, IT CAN BE STOLEN, STORED, AND EVENTUALLY BROKEN. THE ANSWER ISN’T A BETTER KEY. IT’S NO KEY. No retroactive decryption path.
/ DEFINITION
Quantum-resilient Dynamic "Masking".
QLM® protects your encryption without replacing it. Without touching your stack. Without breaking certifications.
Your encryption protects data. QLM® protects encryption itself.
INVISIBLE BY DESIGN. STEALTH BY DEFAULT. UNTOUCHABLE IN OPERATION.
QLM® protects your existing encryption instead of replacing it.
It operates as a lightweight software overlay that masks already-encrypted traffic, ensuring intercepted data remains non-exploitable, now and under post-quantum conditions.
Your systems stay intact. Your protocols stay in place. No rip-and-replace.
Traditional encryption is key-dependent. QLM removes keys entirely. No keys. No key management. Nothing to steal.
Your infrastructure stays.
The threat disappears.
/ PARADIGM SHIFT
Others make keys longer. We found the solution. we removed them entirely.
Not theoretical. Field-ready. Software exists. Works. and Deployable now.
/ KEEP YOUR STACK
Encryption stays. Protocols stay. Infrastructure stays.
/ KEYLESS
No key generation. No exchange. No storage. No rotation. No escrow. Insiders cannot hand over keys that don't exist.
/ HARVEST-PROOF
Capture everything. Decrypt nothing.
No decrypt-later path. Not now. Not post-quantum.
/ INTERCEPT-RESISTANT
No fixed target. No exploit window.
What you analyze is already gone.
/ THE RESULT
Intercept it. Store it. Crack it later. Dead on arrival.
Software-only. Deploys on fielded infrastructure. Zero new hardware.
/ Operationally invisible
near-zero latency, minimal CPU footprint.
No harvest-now, decrypt-later, no keys, no cache, no recovery path. Ever.
/ Multiplatform
OS-agnostic, target-compiled, mission-ready across heterogeneous systems.
/ ZERO RETRAINING
QLM® integrates at the infrastructure layer, transparent to operators and end users.
No new interfaces, no workflow changes, no manual steps.
Protection upgrades. Operations don't.
/ WHAT IT IS
/ DEFINITION TACTICAL COMMS—MADE STEALTH. KEYLESS QUANTUM-RESILIENT STEALTH TUNNEL. A NEW CATEGORY. NOT A NEW CIPHER. NOT A NEW KEY LIFECYCLE. A MASKING LAYER THAT MAKES ENCRYPTED COMMS UNTOUCHABLE—WITHOUT GENERATING, EXCHANGING, STORING, OR MANAGING CRYPTOGRAPHIC KEYS. QLM® DOESN’T REPLACE ENCRYPTION. IT MAKES IT INVISIBLE. UNTOUCHABLE. TURN INTERCEPTION FROM FUTURE BREACH INTO DEAD CAPTURE. / ARCHITECTURE SOFTWARE-ONLY. NEAR-ZERO LATENCY. OS-AGNOSTIC. TARGET-COMPILED. KEYS ARE THE FAILURE MODE. QLM® INTRODUCES NONE. NO GENERATION. NO EXCHANGE. NO STORAGE. NO ESCROW. NOTHING TO STEAL. NOTHING TO HACK. / OPERATIONAL IMPACT NO NEW VENDORS. NO INFRASTRUCTURE SWAP. NO NEW INTERFACES. NO WORKFLOW CHANGES. NO NEW RUNBOOKS. NO TEAMS TO RETRAIN. NO BUDGET SURPRISES. YOUR TEAMS OPERATE EXACTLY AS BEFORE. DAY ONE LOOKS LIKE DAY ZERO. PROTECTION UPGRADES. OPERATIONS DON’T. QUANTUM PROTECTION AS AN OPERATIONAL NON-EVENT. / DEPLOYABLE IN WEEKS, NOT YEARS NOT THEORETICAL. NOT A ROADMAP PROMISE. PRODUCTION-READY. IT DOESN’T ADD COMPLEXITY. IT ADDS STEALTH. / THE RESULT WE REMOVED THE KEY. THE LOCK. AND THE DOOR. THE INDUSTRY IS RACING AGAINST QUANTUM COMPUTE. ALGORITHMS SUNSET. SECURITY WINDOWS SHRINK. ROI SHRINKS WITH THEM. THAT RACE HAS AN EXPIRY DATE. QLM® DOESN’T RACE. IT EXITS THE RACE ENTIRELY. THE FAILURE MODE WAS THE KEY. NO KEY GENERATION. NO EXCHANGE. NO STORAGE. NO ATTACK SURFACE THAT SCALES WITH COMPUTE. RESISTANT BUYS TIME. RESILIENT MAKES ADVERSARY COMPUTE ADVANTAGE IRRELEVANT. QLM® IS QUANTUM-RESILIENT — NOT QUANTUM-RESISTANT. EVERY STORED PACKET STAYS WORTHLESS. TODAY. TOMORROW. POST-QUANTUM. CAPTURE EVERYTHING. DECRYPT NOTHING. REMOVE THE EXPIRY DATE FROM YOUR STACK.
/ HARVEST NOW. DECRYPT LATER. SOLVED.
The Day Stored Data Becomes Readable Is the Day Your Sovereignty Ends
/ THE QUANTUM THREAT
/ LOSE A KEY ONCE YOU LOSE YEARS OF COMMS — RETROACTIVELY. VULNERABLE DOESN’T MEAN WEAK. IT MEANS OBSOLETE. YOUR ALGORITHMS GET SUNSET. YOUR STACKS GET REPLACED. EVEN SUITE A LINEAGES ARE BEING RETIRED. / THE REAL ATTACK IS HAPPENING TODAY YOUR ADVERSARY IS HARVESTING TRAFFIC NOW. STORING EVERYTHING. WAITING FOR QUANTUM TO TURN “CLASSIFIED” INTO “ARCHIVED.” ONE COMPROMISE TURNS TODAY’S INTERCEPTS INTO YEARS OF ARCHIVED EXPOSURE. BY THE TIME QUANTUM BREAKS RSA/ECC AT SCALE, YOUR WINDOW IS CLOSED. NOT JUST TECHNICALLY. CONTRACTUALLY. OPERATIONALLY. POLITICALLY. YOU DON’T NEED “STRONGER” ENCRYPTION. YOU NEED COMMS THAT CAN’T BE DECRYPTED TOMORROW. / IMAGINE A WORLD WHERE YOUR ADVERSARY CAPTURES EVERY PACKET. STORES EVERY FRAME. RUNS IT THROUGH THE MOST ADVANCED QUANTUM PROCESSOR EVER BUILT AND RECOVERS NOTHING. NOT BECAUSE YOUR ENCRYPTION WAS STRONGER. BECAUSE THERE WAS NO KEY TO RECOVER. NO KEY WAS EVER GENERATED. NO KEY WAS EVER EXCHANGED. NO KEY WAS EVER STORED. YOU CAN’T BREAK WHAT DOESN’T EXIST. CAPTURE EVERYTHING. DECRYPT NOTHING. REMOVE THE EXPIRY DATE FROM YOUR STACK — IN WEEKS, NOT YEARS. / STEALTH QUANTUM LAYER STRATEGY THE B-2 STEALTH BOMBER DIDN’T ADD ARMOR. IT BECAME UNDETECTABLE. WE DO THE SAME FOR ENCRYPTED COMMS: NOT STRONGER — STEALTH. AS LONG AS A KEY EXISTS, IT CAN BE STOLEN, STORED, AND EVENTUALLY BROKEN. THE ANSWER ISN’T A BETTER KEY. IT’S NO KEY. No retroactive decryption path.
/ THE QUANTUM THREAT
/ LOSE A KEY ONCE YOU LOSE YEARS OF COMMS — RETROACTIVELY. VULNERABLE DOESN’T MEAN WEAK. IT MEANS OBSOLETE. YOUR ALGORITHMS GET SUNSET. YOUR STACKS GET REPLACED. EVEN SUITE A LINEAGES ARE BEING RETIRED. / THE REAL ATTACK IS HAPPENING TODAY YOUR ADVERSARY IS HARVESTING TRAFFIC NOW. STORING EVERYTHING. WAITING FOR QUANTUM TO TURN “CLASSIFIED” INTO “ARCHIVED.” ONE COMPROMISE TURNS TODAY’S INTERCEPTS INTO YEARS OF ARCHIVED EXPOSURE. BY THE TIME QUANTUM BREAKS RSA/ECC AT SCALE, YOUR WINDOW IS CLOSED. NOT JUST TECHNICALLY. CONTRACTUALLY. OPERATIONALLY. POLITICALLY. YOU DON’T NEED “STRONGER” ENCRYPTION. YOU NEED COMMS THAT CAN’T BE DECRYPTED TOMORROW. / IMAGINE A WORLD WHERE YOUR ADVERSARY CAPTURES EVERY PACKET. STORES EVERY FRAME. RUNS IT THROUGH THE MOST ADVANCED QUANTUM PROCESSOR EVER BUILT AND RECOVERS NOTHING. NOT BECAUSE YOUR ENCRYPTION WAS STRONGER. BECAUSE THERE WAS NO KEY TO RECOVER. NO KEY WAS EVER GENERATED. NO KEY WAS EVER EXCHANGED. NO KEY WAS EVER STORED. YOU CAN’T BREAK WHAT DOESN’T EXIST. CAPTURE EVERYTHING. DECRYPT NOTHING. REMOVE THE EXPIRY DATE FROM YOUR STACK — IN WEEKS, NOT YEARS. / STEALTH QUANTUM LAYER STRATEGY THE B-2 STEALTH BOMBER DIDN’T ADD ARMOR. IT BECAME UNDETECTABLE. WE DO THE SAME FOR ENCRYPTED COMMS: NOT STRONGER — STEALTH. AS LONG AS A KEY EXISTS, IT CAN BE STOLEN, STORED, AND EVENTUALLY BROKEN. THE ANSWER ISN’T A BETTER KEY. IT’S NO KEY. No retroactive decryption path.
/ HARVEST NOW. DECRYPT LATER. SOLVED.
The Day Stored Data Becomes Readable Is the Day Your Sovereignty Ends
/ THE QUANTUM THREAT
/ LOSE A KEY ONCE YOU LOSE YEARS OF COMMS — RETROACTIVELY. VULNERABLE DOESN’T MEAN WEAK. IT MEANS OBSOLETE. YOUR ALGORITHMS GET SUNSET. YOUR STACKS GET REPLACED. EVEN SUITE A LINEAGES ARE BEING RETIRED. / THE REAL ATTACK IS HAPPENING TODAY YOUR ADVERSARY IS HARVESTING TRAFFIC NOW. STORING EVERYTHING. WAITING FOR QUANTUM TO TURN “CLASSIFIED” INTO “ARCHIVED.” ONE COMPROMISE TURNS TODAY’S INTERCEPTS INTO YEARS OF ARCHIVED EXPOSURE. BY THE TIME QUANTUM BREAKS RSA/ECC AT SCALE, YOUR WINDOW IS CLOSED. NOT JUST TECHNICALLY. CONTRACTUALLY. OPERATIONALLY. POLITICALLY. YOU DON’T NEED “STRONGER” ENCRYPTION. YOU NEED COMMS THAT CAN’T BE DECRYPTED TOMORROW. / IMAGINE A WORLD WHERE YOUR ADVERSARY CAPTURES EVERY PACKET. STORES EVERY FRAME. RUNS IT THROUGH THE MOST ADVANCED QUANTUM PROCESSOR EVER BUILT AND RECOVERS NOTHING. NOT BECAUSE YOUR ENCRYPTION WAS STRONGER. BECAUSE THERE WAS NO KEY TO RECOVER. NO KEY WAS EVER GENERATED. NO KEY WAS EVER EXCHANGED. NO KEY WAS EVER STORED. YOU CAN’T BREAK WHAT DOESN’T EXIST. CAPTURE EVERYTHING. DECRYPT NOTHING. REMOVE THE EXPIRY DATE FROM YOUR STACK — IN WEEKS, NOT YEARS. / STEALTH QUANTUM LAYER STRATEGY THE B-2 STEALTH BOMBER DIDN’T ADD ARMOR. IT BECAME UNDETECTABLE. WE DO THE SAME FOR ENCRYPTED COMMS: NOT STRONGER — STEALTH. AS LONG AS A KEY EXISTS, IT CAN BE STOLEN, STORED, AND EVENTUALLY BROKEN. THE ANSWER ISN’T A BETTER KEY. IT’S NO KEY. No retroactive decryption path.
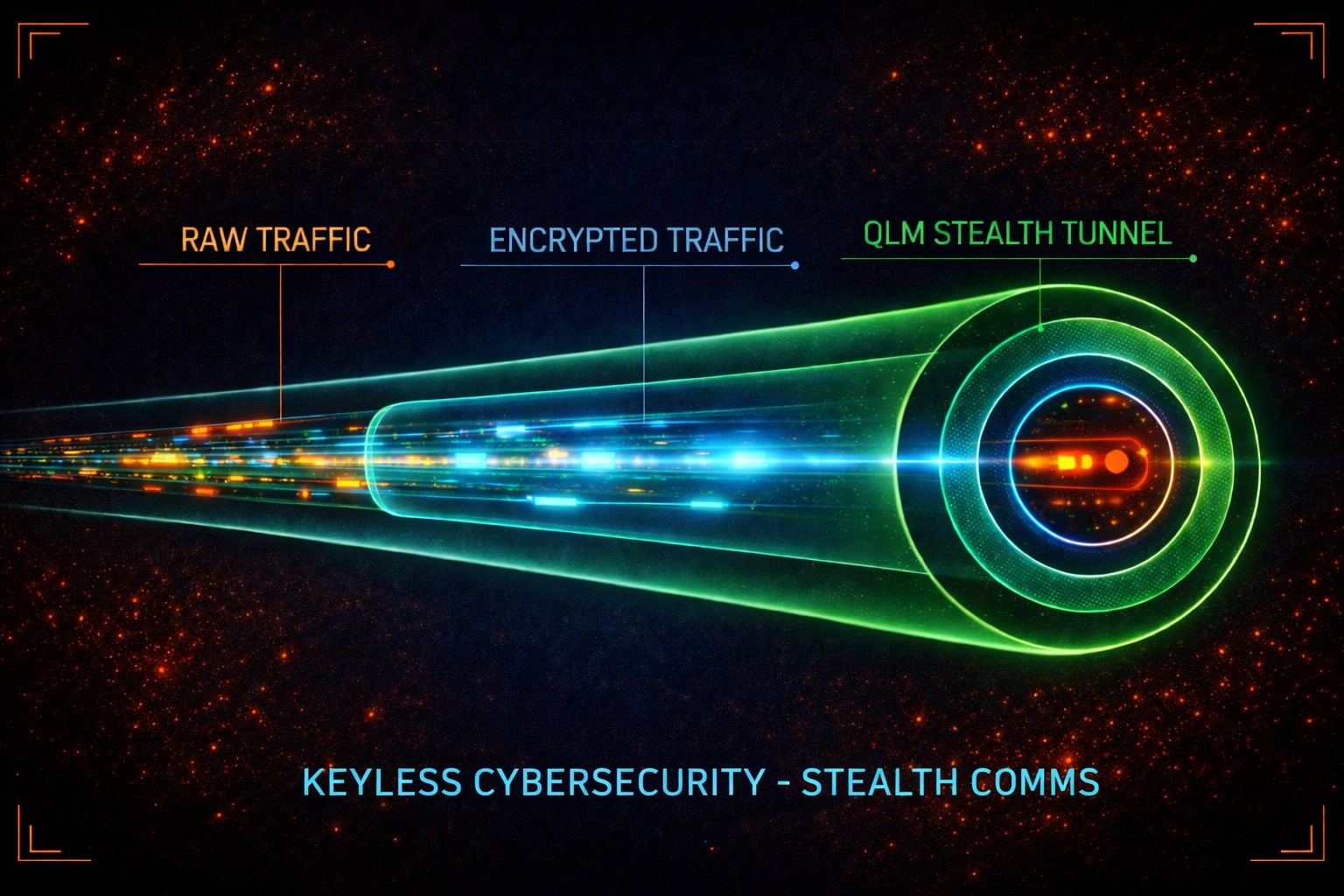
/ QUANTUM LIVE MASK®
Three words. One disruptive model. MILITARY-GRADE. POST-QUANTUM CYBERDEFENSE. QUANTUM LIVE MASK (QLM®) is a keyless, quantum-resilient live-masking layer that wraps your existing encrypted traffic inside a stealth tunnel — with no keys on the wire and no changes to your certified stack. Capture it. No recoverable plaintext. Harvest Now, Decrypt Later. Solved. / QUANTUM Quantum Computers threaten security by targeting key material. We removed the key domain entirely. No keys to steal. No keys to recover. No keys to break. Nothing to hack. / LIVE The mask mutates continuously while traffic is in the air. Synchronized end-to-end, in real time. No stable pattern. No exploit window. Unpredictable. alive. / MASK A keyless channel-level overlay that creates a stealth tunnel around your existing encrypted traffic. No keys on the wire. No rip-and-replace. AES-256. RSA. ECC. Custom crypto. If it's key-based, QLM® wraps it. No session keys in transit. No harvest-now, decrypt-later path. Captured traffic stays worthless.
/ QUANTUM LIVE MASK®
Three words. One disruptive model. MILITARY-GRADE. POST-QUANTUM CYBERDEFENSE. QLM® (Quantum Live Mask) is a keyless, quantum-resilient live-masking layer that wraps your existing encrypted traffic inside a stealth tunnel — with no keys on the wire and no changes to your certified stack. Capture it. No recoverable plaintext. Harvest Now, Decrypt Later. Solved. / QUANTUM Quantum Computers threaten security by targeting key material. We removed the key domain entirely. No keys to steal. No keys to recover. No keys to break. Nothing to hack. / LIVE The mask mutates continuously while traffic is in the air. Synchronized end-to-end, in real time. No stable pattern. No exploit window. Unpredictable. alive. / MASK A keyless channel-level overlay that creates a stealth tunnel around your existing encrypted traffic. No keys on the wire. No rip-and-replace. AES-256. RSA. ECC. Custom crypto. If it's key-based, QLM® wraps it. No session keys in transit. No harvest-now, decrypt-later path. Captured traffic stays worthless.
/ WHAT IT IS
/ DEFINITION TACTICAL COMMS—MADE STEALTH. KEYLESS QUANTUM-RESILIENT STEALTH TUNNEL. A NEW CATEGORY. NOT A NEW CIPHER. NOT A NEW KEY LIFECYCLE. A MASKING LAYER THAT MAKES ENCRYPTED COMMS UNTOUCHABLE—WITHOUT GENERATING, EXCHANGING, STORING, OR MANAGING CRYPTOGRAPHIC KEYS. QLM® DOESN’T REPLACE ENCRYPTION. IT MAKES IT INVISIBLE. UNTOUCHABLE. TURN INTERCEPTION FROM FUTURE BREACH INTO DEAD CAPTURE. / ARCHITECTURE SOFTWARE-ONLY. NEAR-ZERO LATENCY. OS-AGNOSTIC. TARGET-COMPILED. KEYS ARE THE FAILURE MODE. QLM® INTRODUCES NONE. NO GENERATION. NO EXCHANGE. NO STORAGE. NO ESCROW. NOTHING TO STEAL. NOTHING TO HACK. / OPERATIONAL IMPACT NO NEW VENDORS. NO INFRASTRUCTURE SWAP. NO NEW INTERFACES. NO WORKFLOW CHANGES. NO NEW RUNBOOKS. NO TEAMS TO RETRAIN. NO BUDGET SURPRISES. YOUR TEAMS OPERATE EXACTLY AS BEFORE. DAY ONE LOOKS LIKE DAY ZERO. PROTECTION UPGRADES. OPERATIONS DON’T. QUANTUM PROTECTION AS AN OPERATIONAL NON-EVENT. / DEPLOYABLE IN WEEKS, NOT YEARS NOT THEORETICAL. NOT A ROADMAP PROMISE. PRODUCTION-READY. IT DOESN’T ADD COMPLEXITY. IT ADDS STEALTH. / THE RESULT WE REMOVED THE KEY. THE LOCK. AND THE DOOR. THE INDUSTRY IS RACING AGAINST QUANTUM COMPUTE. ALGORITHMS SUNSET. SECURITY WINDOWS SHRINK. ROI SHRINKS WITH THEM. THAT RACE HAS AN EXPIRY DATE. QLM® DOESN’T RACE. IT EXITS THE RACE ENTIRELY. THE FAILURE MODE WAS THE KEY. NO KEY GENERATION. NO EXCHANGE. NO STORAGE. NO ATTACK SURFACE THAT SCALES WITH COMPUTE. RESISTANT BUYS TIME. RESILIENT MAKES ADVERSARY COMPUTE ADVANTAGE IRRELEVANT. QLM® IS QUANTUM-RESILIENT — NOT QUANTUM-RESISTANT. EVERY STORED PACKET STAYS WORTHLESS. TODAY. TOMORROW. POST-QUANTUM. CAPTURE EVERYTHING. DECRYPT NOTHING. REMOVE THE EXPIRY DATE FROM YOUR STACK.
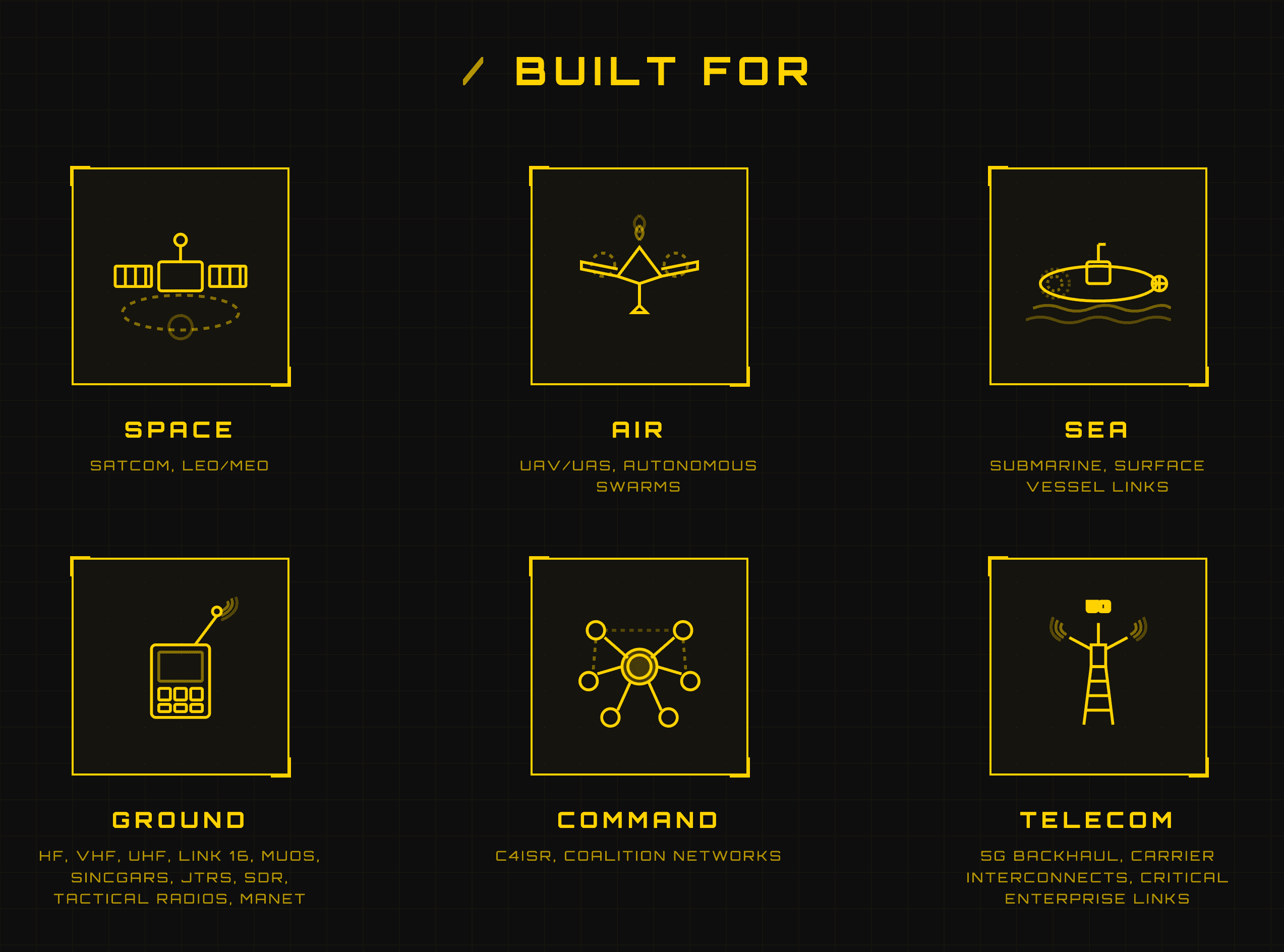
/ TECH OVERVIEW
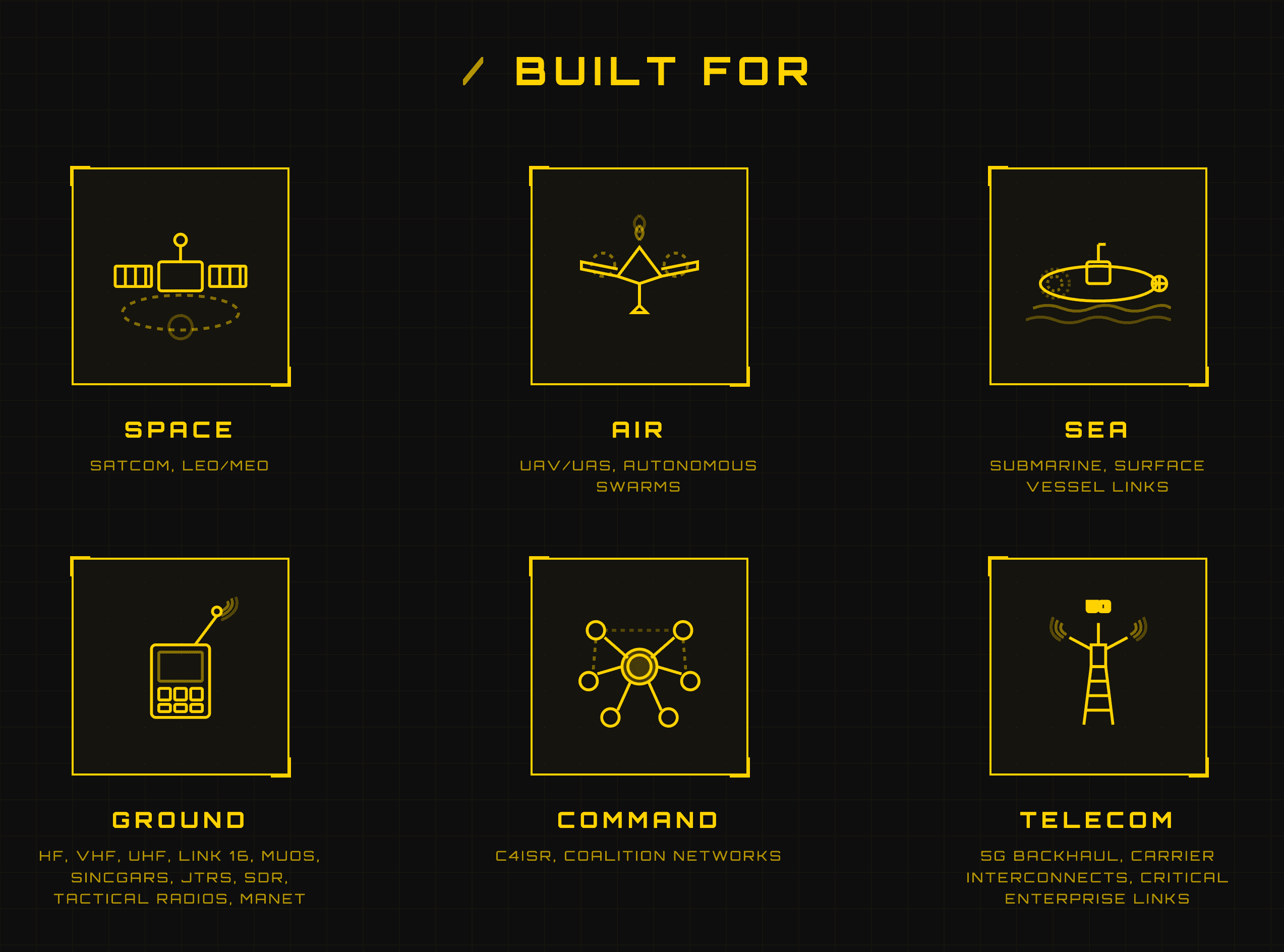
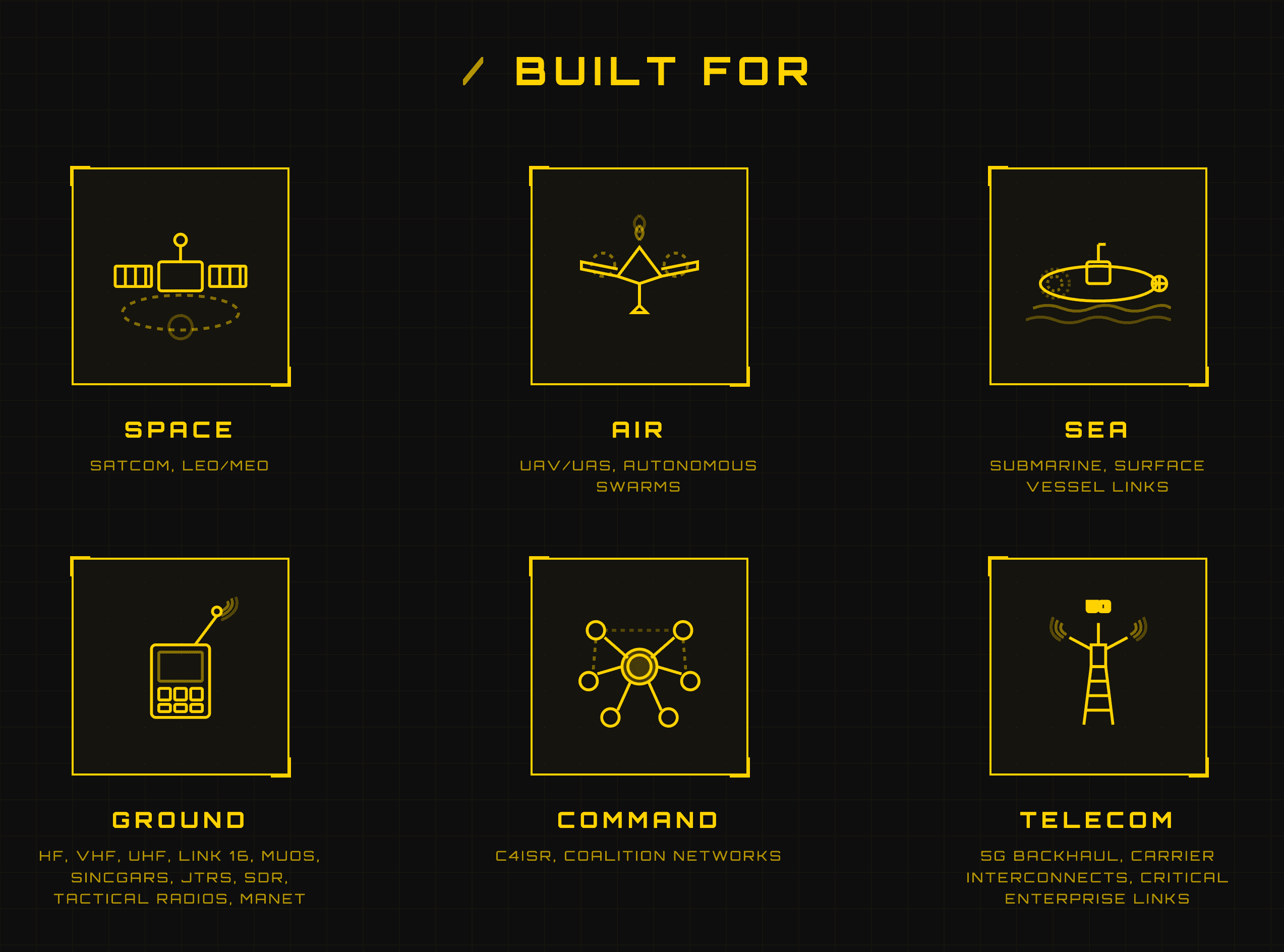
/ NO RE-CERTIFICATION Your certified encryption stays certified. Your certified hardware stays certified. Your operators stay qualified. QLM® overlays your communications nervous system: multi-vendor, multi-domain, legacy to new. C2/C4ISR. Coalition networks. Tactical edge. No algorithm swap. No key-management replacement. Protocol-agnostic. Infrastructure intact. Transparent to operators. Stealth to adversaries. From near-obsolete to mission-ready. / STEALTH FOR C2 STEALTH THE BRAIN. STEALTH THE NERVOUS SYSTEM. C2 is the brain. Comms are the nervous system. Protect the nervous system — protect the decision. One deployable layer across every domain — legacy to modern, vendor to vendor. C2 vendors build the brain. QLM® removes the leverage. No keys. No retrospective compromise. / BUILT FOR Command: C2/C4ISR, coalition networks, joint operations. Ground: HF/VHF/UHF, Link 16, MUOS, SINCGARS, JTRS, SDR, MANET. Air: UAV/UAS, autonomous swarms. Sea: submarine and surface-vessel links. Space: SATCOM, LEO/MEO links. Telecom: 5G backhaul, carrier interconnects, critical enterprise links.
/ TECH OVERVIEW
/ NO RE-CERTIFICATION Your certified encryption stays certified. Your certified hardware stays certified. Your operators stay qualified. QLM® overlays your communications nervous system: multi-vendor, multi-domain, legacy to new. C2/C4ISR. Coalition networks. Tactical edge. No algorithm swap. No key-management replacement. Protocol-agnostic. Infrastructure intact. Transparent to operators. Stealth to adversaries. From near-obsolete to mission-ready. / STEALTH FOR C2 STEALTH THE BRAIN. STEALTH THE NERVOUS SYSTEM. C2 is the brain. Comms are the nervous system. Protect the nervous system — protect the decision. One deployable layer across every domain — legacy to modern, vendor to vendor. C2 vendors build the brain. QLM® removes the leverage. No keys. No retrospective compromise. / BUILT FOR Command: C2/C4ISR, coalition networks, joint operations. Ground: HF/VHF/UHF, Link 16, MUOS, SINCGARS, JTRS, SDR, MANET. Air: UAV/UAS, autonomous swarms. Sea: submarine and surface-vessel links. Space: SATCOM, LEO/MEO links. Telecom: 5G backhaul, carrier interconnects, critical enterprise links.
/ WHAT IT IS
/ DEFINITION TACTICAL COMMS—MADE STEALTH. KEYLESS QUANTUM-RESILIENT STEALTH TUNNEL A NEW CATEGORY. NOT A NEW CIPHER. NOT A NEW KEY LIFECYCLE. A MASKING LAYER THAT MAKES ENCRYPTED COMMS UNTOUCHABLE—WITHOUT GENERATING, EXCHANGING, STORING, OR MANAGING CRYPTOGRAPHIC KEYS. QLM® DOESN’T REPLACE ENCRYPTION. IT MAKES IT INVISIBLE. UNTOUCHABLE. TURN INTERCEPTION FROM FUTURE BREACH INTO DEAD CAPTURE. / ARCHITECTURE SOFTWARE-ONLY. NEAR-ZERO LATENCY. OS-AGNOSTIC. TARGET-COMPILED. KEYS ARE THE FAILURE MODE. QLM® INTRODUCES NONE. NO GENERATION. NO EXCHANGE. NO STORAGE. NO ESCROW. NOTHING TO STEAL. NOTHING TO HACK. / OPERATIONAL IMPACT NO NEW VENDORS. NO INFRASTRUCTURE SWAP. NO NEW INTERFACES. NO WORKFLOW CHANGES. NO NEW RUNBOOKS. NO TEAMS TO RETRAIN. NO BUDGET SURPRISES. YOUR TEAMS OPERATE EXACTLY AS BEFORE. DAY ONE LOOKS LIKE DAY ZERO. PROTECTION UPGRADES. OPERATIONS DON’T. QUANTUM PROTECTION AS AN OPERATIONAL NON-EVENT. / DEPLOYABLE IN WEEKS, NOT YEARS NOT THEORETICAL. NOT A ROADMAP PROMISE. PRODUCTION-READY. IT DOESN’T ADD COMPLEXITY. IT ADDS STEALTH. / THE RESULT WE REMOVED THE KEY. THE LOCK. AND THE DOOR. THE INDUSTRY IS RACING AGAINST QUANTUM COMPUTE. ALGORITHMS SUNSET. SECURITY WINDOWS SHRINK. ROI SHRINKS WITH THEM. THAT RACE HAS AN EXPIRY DATE. QLM® DOESN’T RACE. IT EXITS THE RACE ENTIRELY. THE FAILURE MODE WAS THE KEY. NO KEY GENERATION. NO EXCHANGE. NO STORAGE. NO ATTACK SURFACE THAT SCALES WITH COMPUTE. RESISTANT BUYS TIME. RESILIENT MAKES ADVERSARY COMPUTE ADVANTAGE IRRELEVANT. QLM® IS QUANTUM-RESILIENT — NOT QUANTUM-RESISTANT. EVERY STORED PACKET STAYS WORTHLESS. TODAY. TOMORROW. POST-QUANTUM. CAPTURE EVERYTHING. DECRYPT NOTHING. REMOVE THE EXPIRY DATE FROM YOUR STACK.
/ CONCLUSION
QLM® IS A LIVE, QUANTUM-RESILIENT STEALTH TUNNEL, SOFTWARE-ONLY. OVERLAYS YOUR EXISTING ENCRYPTION. NO NEW HARDWARE. NO APPLIANCES. NO STACK REWRITE. DEVICE SECURITY IS NO LONGER THE FRONTIER. THE CHANNEL IS. A KEYLESS OVERLAY AT THE CHANNEL LEVEL, ON THE WIRE, WRAPPING YOUR ENCRYPTED TRAFFIC, WITH NO STACK CHANGES AND NO SESSION KEYS IN TRANSIT. INTERCEPT THE TRAFFIC. IT YIELDS NO RECOVERABLE PLAINTEXT. DECRYPT-LATER BECOMES IRRELEVANT. NOT A FEATURE. A NEW SECURITY PRIMITIVE. CAPTURED TRAFFIC STAYS WORTHLESS. REMOVE THE EXPIRY DATE FROM YOUR STACK. BECOME QUANTUM-RESILIENT. SOVEREIGN. STEALTH. IN WEEKS, NOT YEARS. Proactive resilience, not reactive defence
/ CONCLUSION
QLM® IS A LIVE, QUANTUM-RESILIENT STEALTH TUNNEL, SOFTWARE-ONLY. OVERLAYS YOUR EXISTING ENCRYPTION. NO NEW HARDWARE. NO APPLIANCES. NO STACK REWRITE. DEVICE SECURITY IS NO LONGER THE FRONTIER. THE CHANNEL IS. A KEYLESS OVERLAY AT THE CHANNEL LEVEL, ON THE WIRE, WRAPPING YOUR ENCRYPTED TRAFFIC, WITH NO STACK CHANGES AND NO SESSION KEYS IN TRANSIT. INTERCEPT THE TRAFFIC. IT YIELDS NO RECOVERABLE PLAINTEXT. DECRYPT-LATER BECOMES IRRELEVANT. NOT A FEATURE. A NEW SECURITY PRIMITIVE. CAPTURED TRAFFIC STAYS WORTHLESS. REMOVE THE EXPIRY DATE FROM YOUR STACK. BECOME QUANTUM-RESILIENT. SOVEREIGN. STEALTH. IN WEEKS, NOT YEARS. Proactive resilience, not reactive defence
QUANTUM
LIVE-MASK
ZERO-KEYS
MASKING
KEYLESS
REALTIME
STEALTH
GO-DARK
OVERLAY
STEALTH
SOVEREIGN
TACTICAL
DEFENSE
ALGORITHM
Resilience
UNTOUCHABLE
HARVEST
POST-QUANTUM
FUTURE-READY
LOW-LATENCY
EXCLUSIVITY
DECRYPT
COMSEC
SECURE COMMS
/ About Quantum Infinity
/ About Quantum Infinity
/ Mission
DEEP DEFENSE TECH. ONE MISSION: END FRAGILE TACTICAL COMMS. WE REMOVED THE KEY DEPENDENCY. HARVEST-NOW / DECRYPT-LATER: SOLVED. WE KNOW HOW IT SOUNDS. DON'T BELIEVE US. ATTACK US. BRING YOUR RED TEAM. YOUR QUANTUM HARDWARE. IF IT HOLDS, YOU'VE FOUND YOUR EDGE.
/ Mission
DEEP DEFENSE TECH. ONE MISSION: END FRAGILE TACTICAL COMMS. WE REMOVED THE KEY DEPENDENCY. HARVEST-NOW / DECRYPT-LATER: SOLVED. WE KNOW HOW IT SOUNDS. DON'T BELIEVE US. ATTACK US. BRING YOUR RED TEAM. YOUR QUANTUM HARDWARE. IF IT HOLDS, YOU'VE FOUND YOUR EDGE.
/ Vision
AS LONG AS COMMS HAVE EXISTED, INTERCEPTION HAS BEEN POSSIBLE. THE ADVANTAGE BELONGED TO WHOEVER COULD STEAL THE SECRET. THAT CHANGES NOW. NO KEYS. NO RECOVERY PATH. NO DECRYPT-LATER. OPERATORS CONTROL COMMS BY DESIGN. SECURITY ISN’T A LAYER YOU BOLT ON. IT’S A CONDITION YOU BUILD IN. THIS ISN’T AN UPGRADE. RETROSPECTIVE COMPROMISE: OBSOLETE.
/ Vision
AS LONG AS COMMS HAVE EXISTED, INTERCEPTION HAS BEEN POSSIBLE. THE ADVANTAGE BELONGED TO WHOEVER COULD STEAL THE SECRET. THAT CHANGES NOW. NO KEYS. NO RECOVERY PATH. NO DECRYPT-LATER. OPERATORS CONTROL COMMS BY DESIGN. SECURITY ISN’T A LAYER YOU BOLT ON. IT’S A CONDITION YOU BUILD IN. THIS ISN’T AN UPGRADE. RETROSPECTIVE COMPROMISE: OBSOLETE.
QUANTUM LIVE MASK®: WHEN BRUTE FORCE BECOMES IRRELEVANT.
/ TECH OVERVIEW
/ NO RE-CERTIFICATION Your certified encryption stays certified. Your certified hardware stays certified. Your operators stay qualified. QLM® overlays your communications nervous system: multi-vendor, multi-domain, legacy to new. C2/C4ISR. Coalition networks. Tactical edge. No algorithm swap. No key-management replacement. Protocol-agnostic. Infrastructure intact. Transparent to operators. Stealth to adversaries. From near-obsolete to mission-ready. / STEALTH FOR C2 STEALTH THE BRAIN. STEALTH THE NERVOUS SYSTEM. C2 is the brain. Comms are the nervous system. Protect the nervous system — protect the decision. One deployable layer across every domain — legacy to modern, vendor to vendor. C2 vendors build the brain. QLM® removes the leverage. No keys. No retrospective compromise. / BUILT FOR Command: C2/C4ISR, coalition networks, joint operations. Ground: HF/VHF/UHF, Link 16, MUOS, SINCGARS, JTRS, SDR, MANET. Air: UAV/UAS, autonomous swarms. Sea: submarine and surface-vessel links. Space: SATCOM, LEO/MEO links. Telecom: 5G backhaul, carrier interconnects, critical enterprise links.
/ CONCLUSION
QLM® IS A LIVE, QUANTUM-RESILIENT STEALTH TUNNEL, SOFTWARE-ONLY. OVERLAYS YOUR EXISTING ENCRYPTION. NO NEW HARDWARE. NO APPLIANCES. NO STACK REWRITE. DEVICE SECURITY IS NO LONGER THE FRONTIER. THE CHANNEL IS. A KEYLESS OVERLAY AT THE CHANNEL LEVEL, ON THE WIRE, WRAPPING YOUR ENCRYPTED TRAFFIC, WITH NO STACK CHANGES AND NO SESSION KEYS IN TRANSIT. INTERCEPT THE TRAFFIC. IT YIELDS NO RECOVERABLE PLAINTEXT. DECRYPT-LATER BECOMES IRRELEVANT. NOT A FEATURE. A NEW SECURITY PRIMITIVE. CAPTURED TRAFFIC STAYS WORTHLESS. REMOVE THE EXPIRY DATE FROM YOUR STACK. BECOME QUANTUM-RESILIENT. SOVEREIGN. STEALTH. IN WEEKS, NOT YEARS. Proactive resilience, not reactive defence
QUANTUM
LIVE-MASK
ZERO-KEYS
MASKING
KEYLESS
REALTIME
STEALTH
GO-DARK
OVERLAY
STEALTH
SOVEREIGN
TACTICAL
DEFENSE
ALGORITHM
Resilience
UNTOUCHABLE
HARVEST
POST-QUANTUM
FUTURE-READY
LOW-LATENCY
EXCLUSIVITY
DECRYPT
COMSEC
SECURE COMMS
/ About Quantum Infinity
/ Mission
DEEP DEFENSE TECH. ONE MISSION: END FRAGILE TACTICAL COMMS. WE REMOVED THE KEY DEPENDENCY. HARVEST-NOW / DECRYPT-LATER: SOLVED. WE KNOW HOW IT SOUNDS. DON'T BELIEVE US. ATTACK US. BRING YOUR RED TEAM. YOUR QUANTUM HARDWARE. IF IT HOLDS, YOU'VE FOUND YOUR EDGE.
/ Vision
For as long as communications have existed, interception has been possible. The advantage has belonged to whoever can steal the secret. That changes now. Operators control their communications by design. No keys. No recovery path. No decrypt-later. Security is no longer a layer you bolt on. It’s a condition you build in. THIS MAKES RETROSPECTIVE COMPROMISE OBSOLETE.
/ How We Work
Industry EXCLUSIVITY
/ PHASE 0: Partnering No end customers. No licenses. No RFPs. We partner only with prime contractors, OEMs, and mission-system integrators. / PHASE 1: Delivery We deliver an MVP of QUANTUM LIVE MASK, proprietary keyless quantum cybersecurity, adapted to your hardware or sector in 90 days or less. Black-box integration. Your brand. Market control in your territory from day one. / PHASE 2: Objective Close the critical vulnerabilities quantum computing will expose before competitors react. QUANTUM MANDATES ARE ACCELERATING. PROCUREMENT IS ALREADY SHIFTING. / PHASE 3: Pilot Validates fit, real-world performance, and global scalability. Pass, we proceed. Fail, we walk away. No ambiguity. / PHASE 4: Attack It Not a pitch. An open challenge. Bring your best quantum computer and best red team. Attack without restrictions. Don’t trust claims. Try to break it. Day and Night. / PHASE 5: Lock It A successful pilot unlocks permanent exclusivity: your vertical, your territory. Not a demo. The gate to a decade of market control. First prime to validate wins. Second gets nothing. Skip 10 years of R&D. The seat is open, briefly.
Pilot first
quantum attack
validate pilot
Industry adaptation
QUANTUM LIVE MASK®: WHEN BRUTE FORCE BECOMES IRRELEVANT.
Industry Pilot
/ PHASE 0: Partnering No end customers. No licenses. No RFPs. We partner only with prime contractors, OEMs, and mission-system integrators. / PHASE 1: Delivery We deliver an MVP of QUANTUM LIVE MASK, proprietary keyless quantum cybersecurity, adapted to your hardware or sector in 90 days or less. Black-box integration. Your brand. Market control in your territory from day one. / PHASE 2: Objective Close the critical vulnerabilities quantum computing will expose before competitors react. QUANTUM MANDATES ARE ACCELERATING. PROCUREMENT IS ALREADY SHIFTING. / PHASE 3: Pilot Validates fit, real-world performance, and global scalability. Pass, we proceed. Fail, we walk away. No ambiguity. / PHASE 4: Attack It Not a pitch. An open challenge. Bring your best quantum computer and best red team. Attack without restrictions. Don’t trust claims. Try to break it. Day and Night. / PHASE 5: Lock It A successful pilot unlocks permanent exclusivity: your vertical, your territory. Not a demo. The gate to a decade of market control. First prime to validate wins. Second gets nothing. Skip 10 years of R&D. The seat is open, briefly.
Pilot first
quantum attack
validate pilot
Industry adaptation
Industry Exclusivity
/ PHASE 6: Exclusivity Grant One industry. One territory. One prime: you. Your technical authority validates the pilot. We grant exclusive commercialization rights. / PHASE 7: Operational Deployment * You deploy to your end users. You capture the revenue. You control the space. We engineer, maintain, and evolve your operational baseline. Your flag. Our engine. No competitor accesses this technology in your vertical. When quantum-proof becomes mandatory, every contract in your sector has one qualified vendor: you. / PHASE 8: Compartmentation Classification: CORE Algorithm. Architecture. Source. Compartmented. Black Box. This is why it works. / PHASE 9: Strategic Position The partner who moves now becomes the category authority in their territory before doctrine is written. First mover owns the vertical. / PHASE 10: Who We Are Mathematicians. Engineers, And Developers. No business development. No sales floor. You are the prime. You win the program. You brief the general. You collect the award. We build what you sell. Royalty-based. ONE PARTNER PER VERTICAL. ONE TERRITORY. FIRST TO VALIDATE SECURES THE SLOT. [CLAIM YOUR SECTOR. BOOK CALL BELOW ↓]
exclusive territory
ROYALTY MODEL
skip r&d
First wins
Industry Exclusivity
/ PHASE 6: Exclusivity Grant One industry. One territory. Your technical authority validates the pilot. / PHASE 7: Operational Deployment * You deploy to your end users. You capture the revenue. You control the space. We engineer, maintain, and evolve. / PHASE 8: Compartmentation Black Box. This is why it works. / PHASE 9: Strategic Position The partner who moves now becomes the category authority. / PHASE 10: Who We Are Mathematicians. Engineers, And Developers. We build what you sell. Royalty-based. ONE PARTNER PER VERTICAL. ONE TERRITORY. [CLAIM YOUR SECTOR. BOOK CALL BELOW ↓]
exclusive territory
ROYALTY MODEL
skip r&d
First wins
Industry Exclusivity
/ PHASE 0: PARTNERING Prime contractors, OEMs, and integrators only. No end customers. No licenses. No RFPs. / PHASE 1: DELIVERY MVP in 90 days. Black-box. Your brand. / PHASE 2: OBJECTIVE Close quantum vulnerabilities before competitors react. / PHASE 3: PILOT Pass, we proceed. Fail, we walk. No ambiguity. / PHASE 4: ATTACK IT Bring your best quantum computer and red team. Don't trust claims. Try to break it. / PHASE 5: LOCK IT First prime to validate wins. / PHASE 6: EXCLUSIVITY One industry. One territory. One prime: you. [CLAIM YOUR SECTOR. BOOK CALL BELOW ↓]
Pilot first
quantum attack
validate pilot
Industry adaptation
.
ONE PARTNER PER INDUSTRY. FIRST TO VALIDATE, LOCKS IN
/ SET THE NEW QUANTUM STANDARD
ONE PARTNER PER INDUSTRY. FIRST TO VALIDATE, LOCKS IN.
QUANTUM
LIVE-MASK
ZERO-KEYS
MASKING
KEYLESS
REALTIME
STEALTH
GO-DARK
OVERLAY
STEALTH
SOVEREIGN
TACTICAL
DEFENSE
ALGORITHM
Resilience
UNTOUCHABLE
HARVEST
POST-QUANTUM
FUTURE-READY
LOW-LATENCY
EXCLUSIVITY
DECRYPT
COMSEC
SECURE COMMS
QUANTUM
LIVEMASK
ZEROKEYS
KEYLESS
MASKING
REALTIME
OVERLAY
STEALTH
SOVEREIGN
TACTICAL
ALGORITHM
RESILIENT
HARVEST
POSTQUANTUM
Resilience
LOWLATENCY
EXCLUSIVITY
DECRYPT
COMSEC
UNTOUCHABLE
SECURE COMMS
Simplicity
UNBREAKABLE
NEW ERA
IF IT CAN BE READ, IT WAS NEVER YOURS. WE MAKE IT UNREADABLE. FOREVER.
IF IT CAN BE READ, IT WAS NEVER YOURS. WE MAKE IT UNREADABLE. FOREVER.
IF IT CAN BE READ, IT WAS NEVER YOURS. WE MAKE IT UNREADABLE. FOREVER.
YOUR COMMUNICATIONS ARE YOUR SOVEREIGNTY. TAKE THEM BACK. PERMANENTLY.
YOUR COMMS ARE YOUR SOVEREIGNTY. TAKE THEM BACK. PERMANENTLY.
/ SET THE NEW QUANTUM STANDARD
ONE PARTNER PER INDUSTRY. FIRST TO VALIDATE, LOCKS IN
THE ENTIRE CYBERSECURITY INDUSTRY HAS BEEN SOLVING THE WRONG PROBLEM FOR DECADES.
THE ENTIRE CYBERSECURITY INDUSTRY HAS BEEN SOLVING THE WRONG PROBLEM FOR DECADES
BUILT ON PHYSICS. BUILT ON MATHEMATICS. NO KEYS. STACK EXPIRY DATE: REMOVED.
BUILT ON PHYSICS. BUILT ON MATHEMATICS. NO KEYS. STACK EXPIRY DATE: REMOVED.
BUILT ON PHYSICS. BUILT ON MATHEMATICS. NO KEYS. STACK EXPIRY DATE: REMOVED.
/ Contact Us